Security isn't a feature — it's a culture
When Fortune 500 companies hesitate about offshore development, security is almost always the top concern. And it's a legitimate one. But the solution isn't avoiding offshore teams — it's implementing the right security architecture from day one.
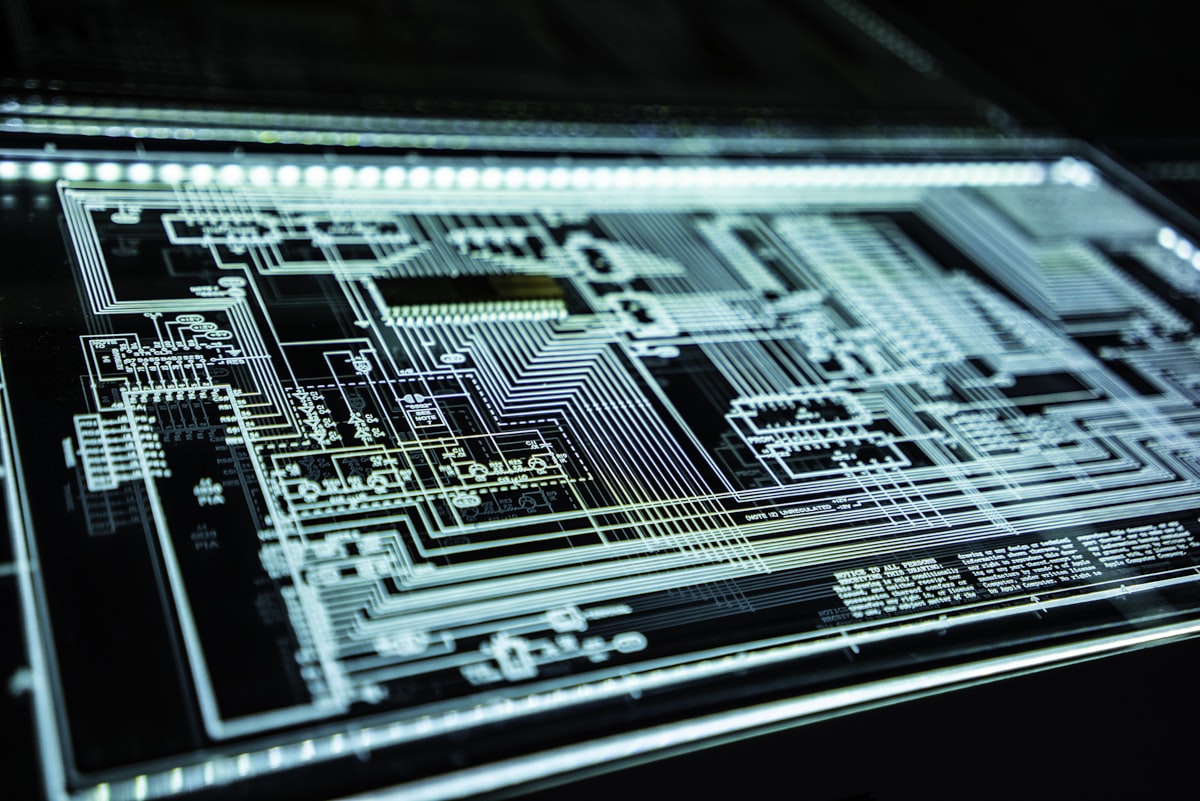
The security stack
1. Zero-trust access controls
Every offshore developer should access your systems through:
- VPN with MFA: No direct access to production systems without multi-factor authentication
- SSO (Single Sign-On): Centralized identity management through Okta, Azure AD, or Google Workspace
- Least-privilege access: Developers get access only to the repos and environments they need
- Time-bound access: Contractor accounts automatically expire and require renewal
2. Code security
- Private repositories: All code in private GitHub/GitLab repos with branch protection
- Mandatory PR reviews: No code merges without at least one review from a senior engineer
- Automated security scanning: Snyk, SonarQube, or GitHub Advanced Security on every PR
- Secrets management: No hardcoded credentials — use Vault, AWS Secrets Manager, or similar
3. Device & endpoint security
- MDM (Mobile Device Management): Company-managed devices or verified BYOD with security policies
- Full disk encryption: Required on all development machines
- Remote wipe capability: Ability to wipe company data if a device is lost or an engagement ends
4. Network security
- Dedicated development environment: Offshore teams work in isolated VPCs/subnets
- No production access: Offshore developers should never have direct production database access
- Audit logging: All access to sensitive systems logged and monitored
Compliance frameworks
Depending on your industry, ensure your offshore partner can demonstrate compliance with:
- SOC 2 Type II: The gold standard for SaaS companies
- ISO 27001: Information security management
- GDPR: If handling EU citizen data
- HIPAA: For healthcare applications
The human element
Technology alone isn't enough. Build security awareness through:
- Quarterly security training for all team members
- Phishing simulation exercises
- Clear incident response procedures
- Security champion program — designate a security-focused engineer on each team
The most secure offshore teams aren't the ones with the most tools — they're the ones where every developer thinks about security as part of their daily work.

Rajat Jain
Full-stack developer and digital marketing expert with over a decade of experience building data-driven platforms.
LinkedIn